In AzureAD, all identities by default have a password expiration. Once a password is expired, it needs to be changed before the account can be used again. For service accounts or resource accounts (example: meeting rooms), this can easily stop the availability of, for example, a Microsoft Teams Room setup like Surface Hub or Logitech Tap.
To see the default settings in your tenant for a certain domain, you can use these Powershell commands:
# Connect to the MS Online service
Connect-MsolService
# Get the domain policy for domain xyz.com
Get-MsolPasswordPolicy -domain xyz.comA typical response could be:
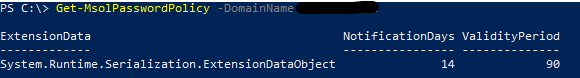
Notificationdays: Specifies the number of days before a user receives notification that their password will expire. (default 14 days)
Validityperiod: Specifies the length of time that a password is valid before it must be changed. (default 90 days)
A domain can only have one policy. You can change the default by using the commandlet “Set-MsolPasswordPolicy”.
Note: When Azure AD Connect synchronizes identities, the synchronized identities are set not to expire and this value can not be changed. These identities will have “DirSyncEnabled” as $true.
Getting and setting the expiration value
A global administrator or user administrator can use PowerShell to set non-synced user passwords not to expire. You can also use PowerShell cmdlets to remove the never-expires configuration or see which user passwords are set to never expire. This setting applies to other providers, such as Intune and Microsoft 365, which rely on AzureAD.
An example is shown below. To see the settings for a user:
Get-AzureADUser -SearchString "<name>" |Select-Object Userprincipalname, PasswordPoliciesIf PasswordPolicies has the value “DisablePasswordExpiration” the password is set to not expire. A blank value means the domain defaults are active.
To check your entire tenant:
Get-AzureADUser -All $true | Select-Object UserPrincipalName, PasswordPoliciesTo disable password expiration (password remains valid forever), you can set the PasswordPolicies:
Set-AzureADUser -ObjectId <user ID> -PasswordPolicies DisablePasswordExpirationTo enable password expiration (password will follow the domain policy), you can remove the PasswordPolicies:
Set-AzureADUser -ObjectId <user ID> -PasswordPolicies None